Table of Contents
ToggleA decade ago, KYC was a compliance ritual.
Today, it’s the invisible infrastructure powering trust in every digital interaction—banking, fintech, lending, wallets, brokerage, insurance, even high-value e-commerce.
The shift is massive.
What once required physical branches, photocopies, in-person signatures, and days of waiting now happens in seconds. A customer uploads an ID, blinks for a liveness check, and—if all is good—steps into a platform instantly.
But behind this seemingly effortless flow is a sophisticated, multi-layered KYC engine quietly doing all the heavy lifting. It evaluates authenticity, checks global risk lists, flags anomalies, and prevents bad actors from slipping through.
In a world where synthetic identities, deepfakes, and cross-border fraud networks are rising rapidly, KYC is no longer optional compliance.
It is risk protection, operational efficiency, and customer safety rolled into one.
This guide breaks down—step-by-step—what an ideal KYC check process should look like in 2025 and beyond.
Why KYC Has Become the Heart of Digital Trust
Modern customers do not care about what happens behind the scenes.
What they do care about is:
- How quickly they can start using a service
- Whether their data is safe
- Whether the platform they are trusting has strong governance
Every onboarding journey—whether for a bank account, UPI wallet, micro-loan, mutual fund, brokerage, or international remittance—depends on the accuracy and flexibility of the KYC framework beneath it.
An ideal KYC system does three things exceptionally well:
- Protects against fraud
- Meets regulatory expectations
- Ensures a smooth, low-friction customer experience
If these three are balanced, conversions go up.
If not, drop-offs rise, manual reviews explode, and fraud becomes harder to contain.
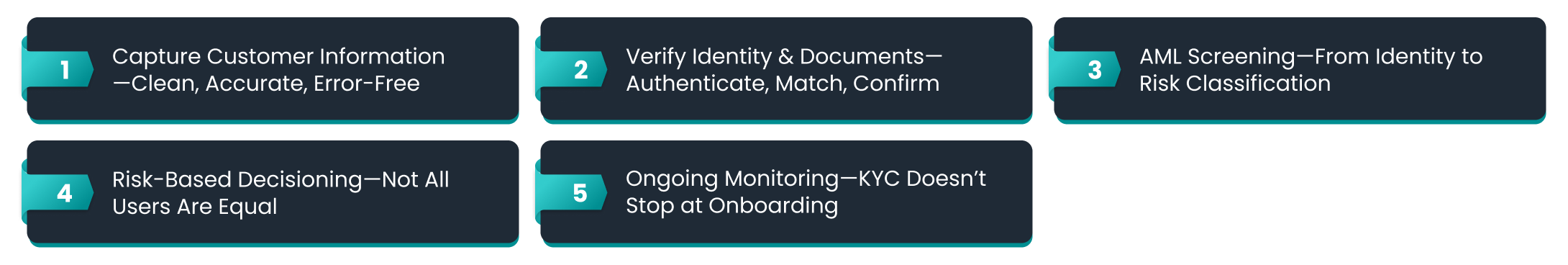
Step 1: Capture Customer Information—Clean, Accurate, Error-Free
Every KYC journey starts with a simple act: data collection.
But this is also the step where errors, inconsistencies, or incomplete information cause the highest downstream friction.
A strong KYC data capture setup must ensure:
- Structure and clarity
- Forms should only ask what is genuinely required.
- Unnecessary fields slow users down.
- Clean formatting
Validations for name, date of birth, address, PIN code, and ID number ensure accuracy before moving forward.
OCR-driven extraction
Instead of relying on customers to type everything correctly, OCR (Optical Character Recognition) can:
Capture text directly from ID images
Convert regional/vernacular text into structured fields
Reduce manual mistakes significantly
Support for non-English IDs
India has dozens of languages appearing on identity documents.
A modern KYC flow must handle this diversity.
For business onboarding, the same principle applies—except the dataset expands:
Registration details
- GST/LLPIN/PAN
- Directors/owners
- UBOs (Ultimate Beneficial Owners)
The takeaway:
Clean data in → smoother KYC pipeline → lower verification costs → fewer manual overrides.
Step 2: Verify Identity & Documents—Authenticate, Match, Confirm
Once customer data is collected, the next layer of KYC begins: validation.
This is the point where an ideal system distinguishes between:
- A real customer
- A forged identity
- A synthetic identity
- A deepfake-generated profile
Identity verification in 2025 is no longer one step—it’s a stack:
1. Document authentication
Detection of tampering, edits, template mismatches
- MRZ validation
- Security feature checks
- Device-level artefact detection
2. OCR-matched consistency
Compare self-entered data with ID data to ensure it’s a match—without relying solely on manual review.
3. Biometric verification
- Face match
- Active/passive liveness
- Deepfake resistance
- Anti-spoofing indicators
This ensures the ID belongs to the person completing onboarding.
4. Device & behavioural intelligence
Detect anomalies like:
- Multiple attempts from the same device
- Proxy/VPN based locations
- Unusual time-of-day patterns
- Rapid “bot-like” submissions
A fraud attempt is rarely a single red flag.
It is often a collection of subtle signals, and modern KYC systems must capture all of them.
Step 3: AML Screening—From Identity to Risk Classification
Verifying “who someone is” is only half the job.
You must also verify:
Should your platform be doing business with this person?
AML (Anti-Money Laundering) screening is the filter that protects platforms from letting transactions flow through individuals who may pose regulatory, financial, or reputational risk.
Ideal AML checks include:
Global Sanctions Screening
Lists from OFAC, UN, HMT, EU, DFAT, Interpol, etc.
PEP Identification
Politically exposed persons require enhanced due diligence.
Adverse Media Analysis
Insights from news, crime reporting, investigations, regulatory filings.
Law Enforcement Watchlists
Databases highlighting individuals under scrutiny or linked to criminal networks.
The challenge?
Sanction updates change constantly.
AML screening must be dynamic—not static.
If the system uses outdated lists, even by a few weeks, risks can slip through unnoticed.
Step 4: Risk-Based Decisioning—Not All Users Are Equal
A powerful KYC process doesn’t treat every customer the same.
It adjusts the flow based on risk level.
This approach is called Risk-Based KYC.
Low-Risk Customers
Minimal friction, instant pass-through.
Examples: salaried individuals with clean identity history.
Medium Risk
Some inconsistencies → secondary checks.
Examples: minor mismatches in document vs. OCR data.
High Risk
Trigger Enhanced Due Diligence (EDD).
Examples:
PEPs
Users from high-risk countries
Mismatch between face and ID
Suspicious device fingerprints
In an ideal setup, decisions are:
- Automated
- Rule-driven
- Consistent
- Explainable
- Audit-friendly
This ensures speed for good users and scrutiny for risky ones.
Step 5: Ongoing Monitoring—KYC Doesn’t Stop at Onboarding
Modern fraud is patient.
Fraudsters behave cleanly during signup and strike later.
This is why ongoing monitoring is a crucial component of ideal KYC checks.
Continuous checks must:
Analyze customer transaction patterns
Sudden spikes, cross-border flows, or behaviour inconsistent with profile.
Update risk scoring
New regulatory alerts → updated internal risk tags.
Trigger reverification
Especially for:
Address changes
High-value transactions
Dormant-to-active accounts
Suspicious patterns
Maintain compliance alignment
Regulators update KYC & AML obligations frequently.
Monitoring ensures alignment doesn’t break.
A strong KYC system is not reactive; it’s anticipatory.
What Happens When KYC Checks Are Built Correctly?
Teams feel it.
Customers feel it.
Regulators notice it.
Fraud metrics reflect it.
Benefits of a well-designed KYC system:
1. Lower Fraud Losses
Fake, stolen, synthetic, and modified identities are blocked early.
2. Higher Conversion Rates
Low-risk customers experience faster, smoother onboarding.
3. Reduced Manual Reviews
Automation handles the predictable patterns & flags only edge cases.
4. Stronger Regulatory Defensibility
Auditable trails, risk scoring, and documented flows.
5. Better Customer Trust
A platform that cares about security earns long-term user confidence.
Best Practices for Building a Frictionless KYC Experience
Here are the principles followed by the most successful digital onboarding teams:
Keep friction proportional
Don’t punish low-risk customers with unnecessary steps.
Use automation strategically
AI/ML for pattern recognition, OCR for extraction, biometrics for identity matching.
Enable dynamic workflows
Let the system adapt based on risk signals.
Invest in ongoing monitoring
Because risks evolve, identities change, and fraud is adaptive.
Treat manual reviews as intelligence
Human reviewers help refine automated logic over time.
Ideal KYC is not about rigidity—it’s about intelligent fluidity.
The Future of KYC: Real-Time, Risk-Aware, and Invisible
The best version of KYC isn’t the one that customers notice.
It’s the one they never think about.
We are moving toward a world where:
- Document verification becomes instant
- Biometrics defeat deepfakes
- Behavioural signals predict fraud before it happens
- AML screening updates in real-time
- Decisioning engines adapt automatically
The KYC of the future will feel like magic to customers, but behind the scenes, it will be pure engineering, compliance science, and risk analytics.
Customer trust is earned through invisible rigor.
Conclusion
KYC checks today are far more than a compliance routine—they form the backbone of trust, safety, and operational resilience across financial services and digital platforms. An ideal KYC framework blends accurate data capture, strong identity verification, robust AML screening, risk-adaptive decisioning, and continuous monitoring into one cohesive flow that protects both users and businesses.
When these layers function together seamlessly, onboarding becomes faster, fraud becomes harder, and trust becomes scalable. The enterprises that invest in comprehensive KYC checks today are the ones that will lead the next wave of digital transformation with confidence and integrity.




Leave a Reply